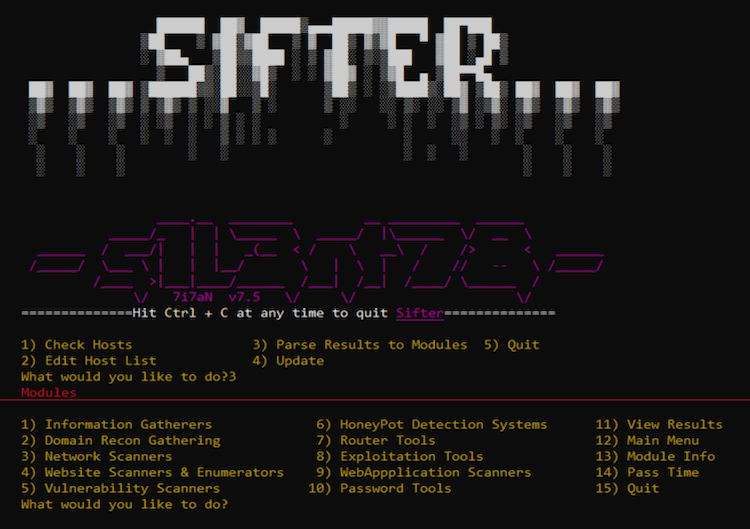
Sifter is a bundle of OSINT, Recon and vulnerability scanner for Penetration Testing.
It combines of Penetration Testing frameworks within different module sets in order to quickly perform recon tasks, check network firewalling, enumerate remote and local hosts, and scan for the ‘blue’ vulnerabilities within microsoft and if unpatched, exploit them. It uses blackwidow and konan for webdir enumeration and attack surface mapping rapidly using ASM.
Gathered info is saved to the results folder, these output files can be easily parsed over to TigerShark in order to be utilised within your campaign, Or compiled for a final report to wrap up a penetration test.
Working on: –
– Kali
– Parrot
– Ubuntu
– Linux (any distro)
Installation:
This will download and install all requirements.
$ git clone https://github.com/s1l3nt78/sifter.git $ cd sifter $ chmod +x install.sh $ ./install.sh
Modules:
Information Modules
= Enterprise Information Gatherers
-theHarvester – https://github.com/laramies/theHarvester
-Osmedeus – https://github.com/j3ssie/Osmedeus
-ReconSpider – https://github.com/bhavsec/reconspider
-CredNinja – -CredNinja – https://github.com/Raikia/CredNinja
= Targeted Information Gatherers
-Maryam – https://github.com/saeeddhqan/Maryam
-Seeker – https://github.com/thewhiteh4t/seeker
-Sherlock – https://github.com/sherlock-project/sherlock
-xRay – https://github.com/evilsocket/xray
# Domain Recon Gathering
-DnsTwist – https://github.com/elceef/dnstwist
-Armory – https://github.com/depthsecurity/armory
-SayDog – https://github.com/saydog/saydog-framework
# Router suits
-MkCheck – https://github.com/s1l3nt78/MkCheck
-RouterSploit – https://github.com/threat9/routersploit
# Exploitation suits
= Microsoft Exploitation suits
-ActiveReign – https://github.com/m8r0wn/ActiveReign
-iSpy – https://github.com/Cyb0r9/ispy
-SMBGhost
–SMBGhost Scanner – https://github.com/ioncube/SMBGhost
–SMBGhost Exploit – https://github.com/chompie1337/SMBGhost_RCE_PoC
= Website Exploitation suits
–Dark Star – https://github.com/s1l3nt78/Dark-Star
–Impulse – https://github.com/LimerBoy/Impulse
-NekoBot – https://github.com/tegal1337/NekoBotV1
-xShock – https://github.com/capture0x/XSHOCK
-VulnX – https://github.com/anouarbensaad/vulnx
= Exploit Searching
-FindSploit – https://github.com/1N3/Findsploit
-ShodanSploit – https://github.com/shodansploit/shodansploit
-TigerShark (Phishing) – https://github.com/s1l3nt78/TigerShark
= Post-Exploitation
-EoP Exploit (Elevation of Priviledge Exploit) – https://github.com/padovah4ck/CVE-2020-0683
-Omega – https://github.com/entynetproject/omega
-WinPwn – https://github.com/S3cur3Th1sSh1t/WinPwn
-CredHarvester – https://github.com/Technowlogy-Pushpender/creds_harvester
-PowerSharp – https://github.com/S3cur3Th1sSh1t/PowerSharpPack
-ACLight2 – https://github.com/cyberark/ACLight
=FuzzyDander – Equation Group, Courtesy of the Shadow Brokers
(Obtained through issue request.)
-FuzzBunch
-Danderspritz
=NevrrMore – This will not be released opensource. This is a private exploitation framework I have
developed. It contains various 0days and other softwares and exploits that I do not want just
anyone to be able to use, this due to the damage it can and will cause.
=BruteDUM (Bruteforcer) – https://github.com/GitHackTools/BruteDum
# Password suits
-Mentalist – https://github.com/sc0tfree/mentalist
-DCipher – https://github.com/k4m4/dcipher
# Network Scanners
-Nmap – https://nmap.org
-AttackSurfaceMapper – https://github.com/superhedgy/AttackSurfaceMapper
-aSnip – https://github.com/harleo/asnip
-wafw00f – https://github.com/EnableSecurity/wafw00f
-Arp-Scan
# HoneyPot Detection Systems
-HoneyCaught – https://github.com/aswinmguptha/HoneyCaught
-SniffingBear – https://github.com/MrSuicideParrot/SniffingBear
-HoneyTel (telnet-iot-honeypot) – https://github.com/Phype/telnet-iot-honeypot
# Vulnerability Scanners
-Flan – https://github.com/cloudflare/flan
-Rapidscan – https://github.com/skavngr/rapidscan
-Yuki-Chan – https://github.com/Yukinoshita47/Yuki-Chan-The-Auto-Pentest
# WebApplication Scanners
-Sitadel – https://github.com/shenril/Sitadel
-OneFind – https://github.com/nyxgeek/onedrive_user_enum
-AapFinder – https://github.com/Technowlogy-Pushpender/aapfinder
-BFAC – https://github.com/mazen160/bfac
-XSStrike – https://github.com/s0md3v/XSStrike
-XSS-Freak – https://github.com/PR0PH3CY33/XSS-Freak
# Website Scanners & Enumerators
-Nikto – https://github.com/sullo/nikto
-Blackwidow – https://github.com/1N3/blackwidow
-Wordpress
—WPScan – https://github.com/wpscanteam/wpscan
—WPForce/Yertle – https://github.com/n00py/WPForce
-Zeus-Scanner – https://github.com/Ekultek/Zeus-Scanner
-Dirb
-DorksEye – https://github.com/BullsEye0/dorks-eye
# Web Mini-Games
– This was added in order to have a fun way to pass time during the more time intensive modules.
Such as nMap Full Port scan or a RapidScan run.
Sifter Help Menu
- $ sifter runs the programs bringing up the menu in a cli environment
- $ sifter -c will check the existing hosts in the hostlist
- $ sifter -a ‘target-ip’ appends the hostname/IP to host file
- $ sifter -m Opens the Main Module menu
- $ sifter -e Opens the Exploitation Modules
- $ sifter -i Opens the Info-based Module menu
- $ sifter -d Opens the Domain Focused Modules
- $ sifter -n Opens the Network Mapping Modules menu
- $ sifter -w Opens the Website Focused Modules
- $ sifter -wa Opens the Web-App Focused Module menu
- $ sifter -p opens the password software for quick passlist generation or hash decryption
- $ sifter -v Opens the Vulnerability Scanning Module Menu
- $ sifter -r Opens the results folder for easy viewing of all saved results
- $ sifter -u Checks for/and installs updates
- $ sifter -h This Help Menu