Hands-on Penetration Testing Labs plus Kali Linux, Snort and Wireshark Bundle.
Real practical hands on hacking skills from a top professional pentester using labs.
Enroll for $65 only – 87% off price on offer
Hands-on Penetration Testing Labs plus Kali Linux, Snort and Wireshark Course Bundle!
This bundle is a set of 7 courses that will give you hands-on exposure to a variety of industry standard tools and methodologies that pertains to offensive and defensive cyber security.
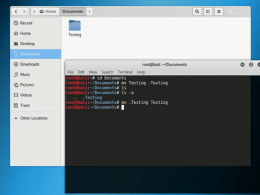
- Kali Linux Hands-on Penetration Testing Labs (1, 2, 3 & 4): These courses consist of one hundred percent hands-on technical labs using Kali Linux to hack a variety of intentionally vulnerable systems.
- Kali Linux Web App Pentesting Labs: This course also consists of one hundred percent hands-on technical labs using Kali Linux. However, the targets are exclusively web applications.
- Snort Intrusion Detection, Rule Writing, and PCAP Analysis: This course has hands-on labs which will show you how to analyze network traffic packet captures, or PCAPs using Wireshark and tcpdump.
- Network Security Analysis Using Wireshark, Snort, and SO: This course completes the course series with a more narrow focus upon analyzing malicious network traffic using industry standard tools like Wireshark, Snort and Security Onion.
What you’ll learn
- Enumerate/scan systems with Netdiscover, Nmap, Dirb, Nikto, Metasploit, Wireshark, etc.
- Perform remote exploitation of systems
- Escalate local privileges to root level
- Utilize a variety of industry standard penetration testing tools within the Kali Linux distro
- Build buffer overflows manually
- Build your own penetration testing lab environment
- Discover vulnerabilities in web applications automatically and manually
- Local and remote buffer overflow
- SQL Injection
- Cross Site Scripting
Requirements
- Familiarity with Windows and Linux
- Basic networking knowledge
- Desktop or Laptop with 8GB RAM (more preferable)
- Windows 7 or 10 host OS preferred (tested)
- Several free and open source VMs and other tools
- Basics IDS knowledge
Description
First of all, this bundle is extremely hands-on. This means we’re not going to be doing much talking about the theory of penetration testing, we’re going to be diving into hands on technical application right away, utilizing industry standard open source technology to hack a variety of intentionally vulnerable operating systems.
All of the resources to build the labs are free. To make the most out of this course, it is recommended that you actually perform the activities within the labs rather than just watch the videos.
We’ll be building a lab environment consisting of Kali Linux, and several intentionally vulnerable web applications including Beebox, SQL injection labs, OWASP Juice Shop, and WebGoat.
We’re also going to cover network security analysis with Wireshark and Tcpdump, intrusion detection system analysis with Snort and Squert, and ethical hacking and penetration testing with various tools on Kali Linux. We will also cover Snort Intrusion Detection, Rule Writing, and PCAP Analysis.
The main points that will be covered in this bundle is enumeration, vulnerability scanning, remote exploitation, buffer overflows, privilege escalation, etc.
These labs will show you how to interpret results from tools such as Nmap, Dirb, and enum4linux, and use them effectively to compromise vulnerable systems.
More specifically, we’ll be going over key essential pentesting skills such as port scanning and service enumeration, local file inclusion, web directory brute forcing, buffer overflows exploit development, SQL injection, Cross-Site Scripting, various types of reverse shells, a variety of local privilege escalation, and much more.
Please note that these labs contain spoilers. I highly encourage independent research and attempting to find answers on your own. This is the single most important skill as a penetration tester, the ability to find solutions to problems you haven’t yet encountered.
Who can join this course for:
- Cybersecurity Students
- Cybersecurity Professionals
- Aspiring Penetration Testers
- CEH Candidates
- OSCP Candidates
- Pentest+ Candidates
Enroll Now
Also See : Cyber Security Online Course 2022 (200+ Courses Bundle) – ENROLL NOW