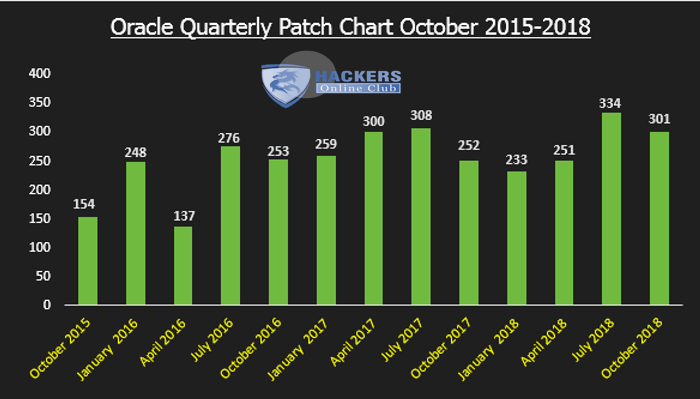
Oracle Patches 301 Security Vulnerabilities in quarterly Critical Patch Update (CPU) Advisory – October 2018 edition
A Critical Patch Update is a collection of patches for multiple security vulnerabilities. Critical Patch Update patches are usually cumulative, but each advisory describes only the security fixes added since the previous Critical Patch Update advisory.
Oracle continues to periodically receive reports of attempts to maliciously exploit vulnerabilities for which Oracle has already released fixes. In some instances, it has been reported that attackers have been successful because targeted customers had failed to apply available Oracle patches. Oracle therefore strongly recommends that customers remain on actively-supported versions and apply Critical Patch Update fixes without delay.
This Critical Patch Update contains 301 new security fixes across the product families listed below.
Affected Products and Patch Information
Note:-
- Vulnerabilities affecting Oracle Database and Oracle Fusion Middleware may affect Oracle Fusion Applications, so Oracle customers should refer to Oracle Fusion Applications Critical Patch Update Knowledge Document, My Oracle Support Note 1967316.1 for information on patches to be applied to Fusion Application environments.
Due to the threat posed by a successful attack, Oracle strongly recommends that customers apply Critical Patch Update fixes as soon as possible. Until you apply the Critical Patch Update fixes, it may be possible to reduce the risk of successful attack by blocking network protocols required by an attack.
For attacks that require certain privileges or access to certain packages, removing the privileges or the ability to access the packages from users that do not need the privileges may help reduce the risk of successful attack. Both approaches may break application functionality, so Oracle strongly recommends that customers test changes on non-production systems. Neither approach should be considered a long-term solution as neither corrects the underlying problem.
Vulnerabilities affecting Oracle Solaris may affect Oracle ZFSSA so Oracle customers should refer to the Oracle and Sun Systems Product Suite Critical Patch Update Knowledge Document, My Oracle Support Note 2160904.1 for information on minimum revisions of security fixes required to resolve ZFSSA issues published in Critical Patch Updates and Solaris Third Party bulletins.
Users running Java SE with a browser can download the latest release from JAVA website. Users on the Windows and Mac OS X platforms can also use automatic updates to get the latest release
Oracle conducts an analysis of each security vulnerability addressed by a Critical Patch Update. Oracle does not disclose detailed information about this security analysis to customers, but the resulting Risk Matrix and associated documentation provide information about the type of vulnerability, the conditions required to exploit it, and the potential impact of a successful exploit.
Oracle provides this information, in part, so that customers may conduct their own risk analysis based on the particulars of their product usage. For more information, see Oracle vulnerability disclosure policies.
The protocol in the risk matrix implies that all of its secure variants (if applicable) are affected as well. For example, if HTTP is listed as an affected protocol, it implies that HTTPS (if applicable) is also affected. The secure variant of a protocol is listed in the risk matrix only if it is the only variant affected, e.g. HTTPS will typically be listed for vulnerabilities in SSL and TLS.
Oracle Database Server Risk Matrix
This Critical Patch Update contains 7 new security fixes for the Oracle Database Server divided as follows:
- 3 new security fixes for the Oracle Database Server. 2 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. None of these fixes are applicable to client-only installations, i.e., installations that do not have the Oracle Database Server installed.
- 1 new security fix for Oracle Big Data Graph. This vulnerability is remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. The English text form of this Risk Matrix can be found here.
- 3 new security fixes for Oracle GoldenGate. All of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Following Oracle Risk Matrix vulnerabilities is remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle Risk Matrix Vulnerabilities
This Critical Patch Update contains 1 new security fix for Oracle Big Data Graph.
Oracle GoldenGate Risk Matrix
This Critical Patch Update contains 3 new security fixes for Oracle GoldenGate. All of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle Communications Applications Risk Matrix
This Critical Patch Update contains 14 new security fixes for Oracle Communications Applications. 9 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle Construction and Engineering Suite Risk Matrix
This Critical Patch Update contains 10 new security fixes for the Oracle Construction and Engineering Suite. 9 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle E-Business Suite Risk Matrix
This Critical Patch Update contains 16 new security fixes for the Oracle E-Business Suite. 14 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle E-Business Suite products include Oracle Database and Oracle Fusion Middleware components that are affected by the vulnerabilities listed in the Oracle Database and Oracle Fusion Middleware sections. The exposure of Oracle E-Business Suite products is dependent on the Oracle Database and Oracle Fusion Middleware versions being used.
Oracle Database and Oracle Fusion Middleware security fixes are not listed in the Oracle E-Business Suite risk matrix. However, since vulnerabilities affecting Oracle Database and Oracle Fusion Middleware versions may affect Oracle E-Business Suite products, Oracle recommends that customers apply the October 2018 Critical Patch Update to the Oracle Database and Oracle Fusion Middleware components of Oracle E-Business Suite.
For information on what patches need to be applied to your environments, refer to Oracle E-Business Suite Release 12 Critical Patch Update Knowledge Document (October 2018)
Oracle Enterprise Manager Products Suite Risk Matrix
This Critical Patch Update contains 4 new security fixes for the Oracle Enterprise Manager Products Suite. 3 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. None of these fixes are applicable to client-only installations, i.e., installations that do not have the Oracle Enterprise Manager Products Suite installed.
Oracle Financial Services Applications Risk Matrix
This Critical Patch Update contains 2 new security fixes for Oracle Financial Services Applications. Both of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle Java SE Risk Matrix
This Critical Patch Update contains 12 new security fixes for Oracle Java SE. 11 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials. The English text form of this Risk Matrix can be found here.
The CVSS scores below assume that a user running a Java applet or Java Web Start application (in Java SE 8) has administrator privileges (typical on Windows). When the user does not run with administrator privileges (typical on Solaris and Linux), the corresponding CVSS impact scores for Confidentiality, Integrity, and Availability are “Low” instead of “High”, lowering the CVSS Base Score. For example, a Base Score of 9.6 becomes 7.1.
Oracle MySQL Risk Matrix
This Critical Patch Update contains 38 new security fixes for Oracle MySQL. 3 of these vulnerabilities may be remotely exploitable without authentication, i.e., may be exploited over a network without requiring user credentials.
Oracle strongly recommends that customers apply security fixes as soon as possible.