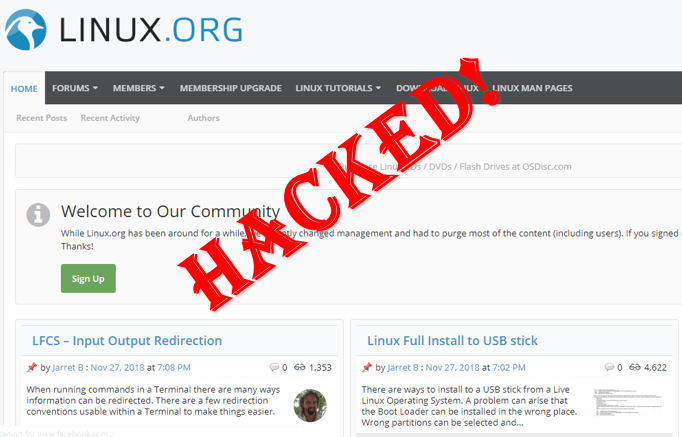
Hackers attack on Linux.org domain and hacked through DNS Hijacking Technique.
The website defaced by hackers and redirect to other website. The administrator of website have lost control of the domain for several hours.
The Hackers Defaced the website with message
Linux.org domain is not official website of Linux, but it is the platform where users discussing and resolving their Linux related issues.
What is DNS Hijacking?
DNS hijacking or DNS redirection, a technique that involves redirecting to malicious website by changing their DNS address so that visitor redirect to other website as behalf of particular website.
The Cyber attackers redirects users through the use of a rogue DNS server or other strategy that changes the IP address.
On Reddit Linux.org Confirmed,
"Linux.org goings on This evening someone got into my partner's netsol account and pointed linux.org DNS to their own cloudflare account. The production env (web / db) wasn't touched. DNS was simply pointing to another box. She's working with netsol to prove ownership, etc.. and we're hoping things will be cleared up in the morning.Lesson learned - MFA all the things. We hope to be back soon. I'm happy to answer any questions on this.. Mainly I wanted to drive home that the actual linux.org servers were untouched and no data was leaked. Props to these guys for digging out the password to my partner's netsol acct, but all of our users' data is safe. Thanks guys."
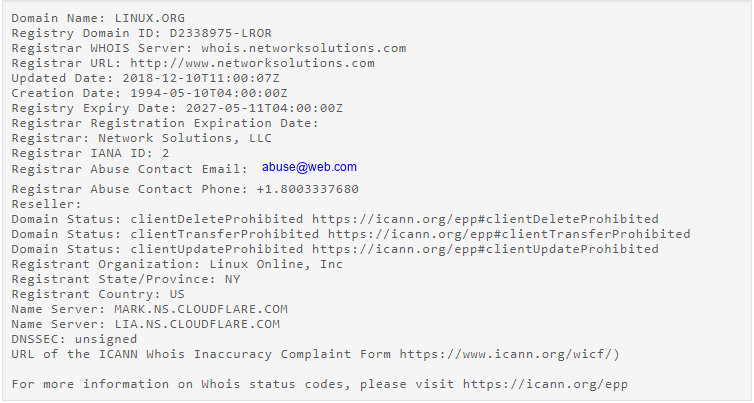
According to Whois record, the domain has been updated on 10th December 2018. Cloudflare blocked the rogue server and returned Linux.org control to its real admins.
One of the Linux website administrator wrote,
“Yesterday afternoon around 5pm EST someone was able to get into the registrar account for our domain and point DNS to another server – as well as lock us out from changing it.
They pointed the domain name to a pretty rude page for most of the evening until CloudFlare stepped in and blocked the domain for us.
After a lot of back and forth with our registrar, we were able to get things back under our control. I’d like to point out that our server environment was not touched so there are no worries about your data.
We’ve gone over security protocols and are tightening things up that may have slipped through in the past.
Thanks for your support!”