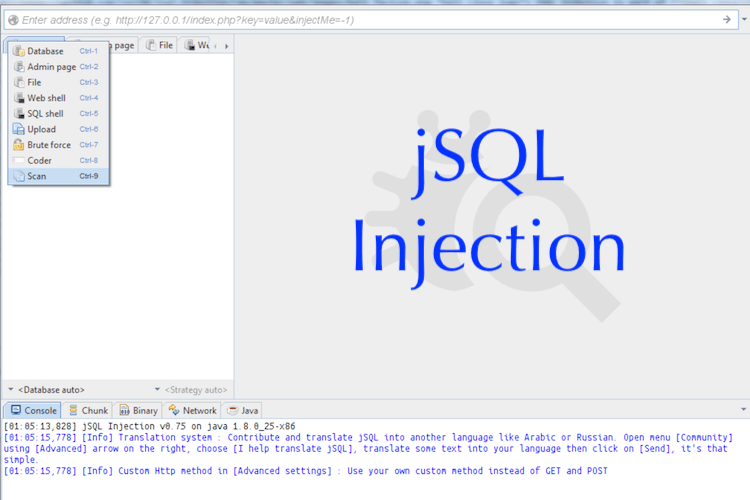
jSQL Injection, an Open Source Java Based Automatic SQL database Injection Software.
It is free an open source and cross-platform for Windows, Linux, Mac OS X. Also a lightweight application used to find database information from a distant server with speed.
jSQL Injection is also part of the official penetration testing distribution Kali Linux and is included in other distributions like Pentest Box, Parrot Security OS, ArchStrike or BlackArch Linux.
This software is developed using open source libraries like Spring, Spock and Hibernate, and it uses platform Travis CI for continuous integration.
Each program update is tested in the cloud on Travis CI using Java version 8 through 13, and against various MySQL, PostgreSQL and H2 databases. Source code is open to pull request and to any contribution about multi-threading, devops, optimization, unit and integration tests.
Features
- Automatic injection of 34 kinds of databases: Access, Altibase, C-treeACE, CockroachDB, CUBRID, DB2, Derby, Exasol, Firebird, FrontBase, H2, Hana, HSQLDB, Informix, Ingres, InterSystems-IRIS, MaxDB, Mckoi, MemSQL, MimerSQL, MonetDB, MySQL, Neo4j, Netezza, NuoDB, Oracle, PostgreSQL, Presto, SQLite, SQL Server, Sybase, Teradata and Vertica
- Multiple injection strategies: Normal, Error, Stacked, Blind and Time
- Various injection processes: Default, Zip, Dios
- Sandbox for SQL and tampering scripting
- List to inject multiple targets
- Read and write file using injection
- Create and display Web shell and SQL shell
- Bruteforce password hash
- Search for admin pages
- Hash, encode and decode text
- Authenticate using Basic, Digest, NTLM and Kerberos
- Proxy connection on HTTP, SOCKS4 and SOCKS5
Install Java 8 up to Java 15, then download the latest release and double-click on the file jsql-injection-v0.82.jar to launch the software. You can also type java -jar jsql-injection-v0.82.jar in your terminal to start the program.
If you are using Kali Linux then get the latest release using command sudo apt-get -f install jsql, or make a system full upgrade with apt update then apt full-upgrade.
[Test-bed scripts]
Use the sample scripts to test injection on your local environment. First install a development environment like EasyPHP, then download the test-bed PHP scripts and place them into www/.
<?php
# http://127.0.0.1/mysql/strategy/get-normal.php?id=0
$link = mysqli_connect('localhost', 'root', '', 'my_database');
$result = $link->query("SELECT col1, col2 FROM my_table where id=$_GET[id]");
while ($row = $result->fetch_array($result, MYSQLI_NUM))
echo join(',', $row);[Roadmap]
Full Path Disclosure, Injection strategies: routed query, WAF detection
In progress
Fingerprint database and insertion char, Custom rows load
Since latest release
New Strategy Dump In One Shot
– New preferences for Threads, User-Agent, CSRF, Query size reduction
– Add Stacked query and new Error strategies, Database and char insertion identification
– New databases: Altibase C-treeACE Exasol FrontBase InterSystems-IRIS MemSQL MimerSQL MonetDB Netezza Presto.
Change log
- v0.82 Tampering options, Refactoring for Cloud and multithreading compatibility
- v0.81 Test all parameters including JSON, Parse forms and Csrf tokens, Databases: CockroachDB Mckoi Neo4j NuoDB Hana and Vertica, Translation complete: Russian, Chinese
- v0.79 Error Strategies for MySQL and PostgreSQL compatible with Order/Group By, Wider range of Characters Insertion including multibyte %bf
- v0.78 SQL Engine, MySQL Error strategy: DOUBLE, Translations: es pt de it nl id, 18 Database flavors including Access
- v0.76 Translation: cz, 17 Database flavors including SQLite
- v0.75 URI injection point, Source code mavenification, Upgrade to Java 7
- v0.73 Authentication: Basic Digest Negotiate NTLM and Kerberos, Database flavor selection
- v0.7 Scan multiple URLs, Github Issue reporter, 16 Database flavors including Cubrid Derby H2 HSQLDB MariaDB and Teradata
- alpha-v0.6 Speed x2: No more hex encoding, 10 Database flavors including MySQL Oracle SQLServer PostgreSQL DB2 Firebird Informix Ingres MaxDb and Sybase, JUnit tests, Log4j, GUI translation
- 0.5 SQL Shell, File Uploader
- 0.4 Admin page finder, Bruteforce hashes like MD5 and MySQL, Encode and decode string with methods like Base64, Hex and MD5
- 0.3 File injection, Web Shell with integrated CLI, Persistence of application parameters, Update checker
- 0.2 Strategy Time, Multi-thread control: Start Pause Resume and Stop, Log URL calls
- 0.0-0.1 Method GET POST Header and Cookie, Strategies Normal Error and Blind, Best strategy selection, Progression bars, Simple evasion, Proxy settings, MySQL only
Disclaimer
Attacking web-server is illegal without prior mutual consent. The end user is responsible and obeys all applicable laws. Developers assume no liability and are not responsible for any misuse or damage caused by this program.