The security researchers have discovered a new surveillance app targets iPhones users.
The mobile security firm Lookout found the malicious app, said its developer abused their Apple-issued enterprise certificates to bypass the tech giant’s app store to infect the victims.
Once the app installed, it can able to grab victims contacts, recording, photos, videos, real time location and other private information. It can be accessed remotely.
Security researchers found that the malicious app was spread through fake sites to be cell carriers in Italy and Turkmenistan. To make that possible, the operators of the Exodus appear to have abused Apple’s Developer Enterprise Program, a provisioning mechanism that allows enterprises to distribute proprietary in-house iOS apps to employees without having to use Apple’s mobile app store.
Same app used for Android Surveillance previously
Same kind of app previously discovered in Android given named Exodus. Which has developed by the same Italian Surveillance app maker Connexxa, a known provider of surveillance tools to Italian authorities.
According to Lookout blog,
Early last year, Lookout discovered a sophisticated Android surveillanceware agent that appears to have been created for the lawful intercept market. The agent appears to have been under development for at least five years and consists of three stages.
First, there is a small dropper, then a large second stage payload that contains multiple binaries (where most of the surveillance functionality is implemented), and finally a third stage which typically uses the DirtyCOW exploit (CVE-2016-5195) to obtain root. Security Without Borders has recently published an analysis of this family.
It was capable of rooting Android devices and possessed an advanced set of spying features that gave attackers full control of infected devices.
The apps themselves pretended to be carrier assistance apps which instructed the user to “keep the app installed on your device and stay under Wi-Fi coverage to be contacted by one of our operators”.
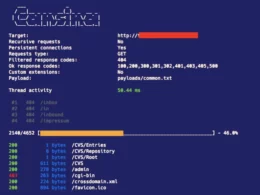
Though different versions of the app vary in structure, malicious code was initialized at application launch without the user’s knowledge, and a number of timers were setup to gather and upload data periodically.
Upload data was queued and transmitted via HTTP PUT requests to an endpoint on the C2. The iOS apps leverage the same C2 infrastructure as the Android version and use similar communications protocols. Push notifications were also used to control audio recording.
This week, Kaspersky Security summit in Singapore, Lookout security researchers will give the presentation on malicious iOS App known as Exodus.