Bug found in latest iOS version 13.4, and preventing VPNs connection from Encrypting all device traffic.
The iOS bug was found by ProtonVPN security researchers, it can lead to data leaks.
How the iOS VPN bypass vulnerability works?
Typically, when you connect to a virtual private network (VPN), the operating system of your device closes all existing Internet connections and then re-establishes them through the VPN tunnel.
The VPN bypass vulnerability could result in users’ data being exposed if the affected connections are not encrypted themselves (though this would be unusual nowadays). The more common problem is IP leaks. An attacker could see the users’ IP address and the IP address of the servers they’re connecting to. Additionally, the server you connect to would be able to see your true IP address rather than that of the VPN server.
How the researchers found iOS Bug?
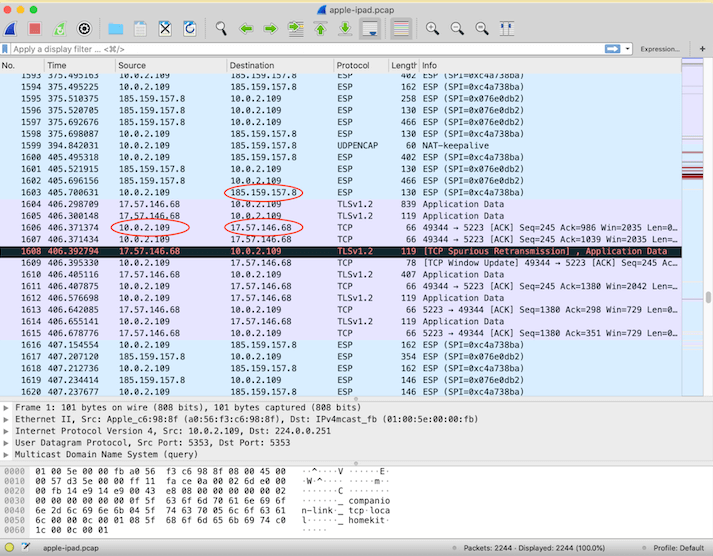
To investigate this issue, security researchers used Wireshark to capture an iOS device’s network traffic.
When you connect a device to VPN, you should only be able to see traffic between the device’s IP and the VPN server or local IP addresses (other devices on your local network). As the capture below shows, there is also direct traffic between the iOS device’s IP and an external IP address that is not the VPN server (in this case it’s an Apple server).
Here :
- 10.0.2.109 = iOS device’s IP address
- 185.159.157.8 = ProtonVPN server
- 17.57.146.68 = Apple-owned IP address
How to iOS VPN bypass vulnerability Works?
Internet connections established after you connect to VPN are not affected. But connections that are already running when you connect to VPN may continue outside the VPN tunnel indefinitely. There is no way to guarantee that those connections will be closed at the moment you start a VPN connection.
However, the researchers have discovered the following technique to be almost as effective:
- Connect to any ProtonVPN server.
- Turn on airplane mode: This will kill all Internet connections and temporarily disconnect ProtonVPN.
- Turn off airplane mode: ProtonVPN will reconnect, and your other connections should also reconnect inside the VPN tunnel, though they cannot guarantee this 100 percent works.
Alternatively, Apple recommends using Always-on VPN to mitigate this issue. This method requires using device management, so unfortunately it doesn’t mitigate the issue for third-party applications such as ProtonVPN.
Now Apple is known the Bug and still working to fix it.











