The security researcher found 20 Vulnerabilities in Samsung IoT devices. Which are allowing cyber attackers to remotely control, smart-things Hub via IP cameras.
The vulnerabilities were discovered by Claudio Bozzato of Cisco Talos.
The researcher found three notable chain the last of which allows for remotely compromising the device without prior authentication.
-
Remote code execution
-
Remote information leakage
-
Pre-auth remote code execution
In the description of notable chains, the researcher defines multiple vectors, to achieve code execution from the network. An attacker can obtain a memory dump of the `hubCore` process, which contains most of the core logic, and consequently sensitive information, of the Hub.
An attacker can compromise the device remotely without prior authentication. Note that other similar vulnerabilities could be used as the last element of the chain. However, they might be more complex to implement.
According to Cisco Talos blog,
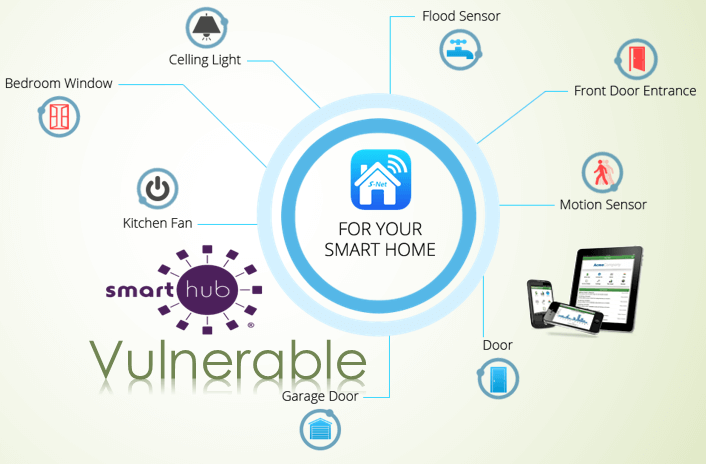
The SmartThings Hub is a central controller that monitors and manages various internet-of-things (IoT) devices such as smart plugs, LED light bulbs, thermostats, cameras, and more that would typically be deployed in a smart home. The SmartThings Hub functions as a centralized controller for these devices and allows users to remotely connect to and manage these devices using a smartphone.
The firmware running on the SmartThings Hub is Linux-based and allows for communications with IoT devices using a variety of different technologies such as Ethernet, Zigbee, Z-Wave and Bluetooth.
What Vulnerabilities Can Do?
- Smart locks controlled by the SmartThings Hub could be unlocked, allowing for physical access to the home.
Cameras deployed within the home could be used to remotely monitor occupants. - The motion detectors used by the home alarm system could be disabled.
- Smart plugs could be controlled to turn off or on different things that may be connected.
- Thermostats could be controlled by unauthorized attackers.
- Attackers could cause physical damage to appliances or other devices that may be connected to smart plugs deployed within the smart home.
Following Vulnerabilities have been found
- Samsung SmartThings Hub RTSP Password Command Injection Vulnerability (TALOS-2018-0539 / CVE-2018-3856)
- Samsung SmartThings Hub video-core samsungWifiScan Code Execution Vulnerability (TALOS-2018-0548 / CVE-2018-3863 – CVE-2018-3866)
- Samsung SmartThings Hub video-core samsungWifiScan Callback Code Execution Vulnerability (TALOS-2018-0549 / CVE-2018-3867)
- Samsung SmartThings Hub video-core credentials videoHostUrl Code Execution Vulnerability (TALOS-2018-0554 / CVE-2018-3872)
- Samsung SmartThings Hub video-core credentials Code Execution Vulnerability (TALOS-2018-0555 / CVE-2018-3873 – CVE-2018-3878)
- Samsung SmartThings Hub video-core credentials Parsing SQL Injection Vulnerability (TALOS-2018-0556 / CVE-2018-3879)
- Samsung SmartThings Hub video-core Database find-by-cameraId Code Execution Vulnerability (TALOS-2018-0557 / CVE-2018-3880)
- Samsung SmartThings Hub video-core clips Code Execution Vulnerability (TALOS-2018-0570 / CVE-2018-3893 – CVE-2018-3897)
- Samsung SmartThings Hub video-core Camera URL Replace Code Execution Vulnerability (TALOS-2018-0573 / CVE-2018-3902)
- Samsung SmartThings Hub video-core Camera Update Code Execution Vulnerabilities (TALOS-2018-0574 / CVE-2018-3903 – CVE-2018-3904)
- Samsung SmartThings Hub video-core Camera Creation Code Execution Vulnerability (TALOS-2018-0575 / CVE-2018-3905)
- Samsung SmartThings Hub video-core Database shard.videoHostURL Code Execution Vulnerability (TALOS-2018-0576 / CVE-2018-3906)
- Samsung SmartThings Hub video-core REST Request Parser HTTP Pipelining Injection Vulnerabilities (TALOS-2018-0577 / CVE-2018-3907 – CVE-2018-3909)
- Samsung SmartThings Hub hubCore Port 39500 HTTP Header Injection Vulnerability (TALOS-2018-0578 / CVE-2018-3911)
- Samsung SmartThings Hub video-core Database shard Code Execution Vulnerabilities (TALOS-2018-0581 / CVE-2018-3912 – CVE-2018-3917)
- Samsung SmartThings Hub hubCore Port 39500 Sync Denial Of Service Vulnerability (TALOS-2018-0582 / CVE-2018-3918)
- Samsung SmartThings Hub video-core Database clips Code Execution Vulnerability (TALOS-2018-0583 / CVE-2018-3919)
- Samsung SmartThings Hub video-core AWSELB Cookie Code Execution Vulnerability (TALOS-2018-0591 / CVE-2018-3925)
- Samsung SmartThings Hub hubCore ZigBee firmware update CRC16 check Denial of Service Vulnerability (TALOS-2018-0593 / CVE-2018-3926)
- Samsung SmartThings Hub hubCore Google Breakpad backtrace.io information disclosure vulnerability (TALOS-2018-0594 / CVE-2018-3927)
All Vulnerabilities have been Patched
A Samsung spokesperson told Threatpost patches have been deployed that fix the bugs.
“We are aware of the security vulnerabilities for SmartThings Hub V2 and released a patch for automatic update to address the issue. All active SmartThings Hub V2 devices in the market are updated to date,” Samsung said.