Today, i am going to show you many aspects of the Windows Password Storage path, Method of Encryption, and breaking into Windows by cracking the admin password. We need this often for many reasons:
1) Sometime we have forgotten our old password and Hint isn’t helping out.
2) We want to break into someone computer to get the information.
3) Just want to take revenge from someone.
4) Stealing computer data.
Lets, take a deep dive in Cracking Windows password and also where these are stored and in which format.
SAM file and Password Hashes~Place where these passwords are stored in Hashes:
Password Hashes – When you type your password into a Windows NT, 2000, or XP login Windows Seven, Vista etc Windows encrypts your password using a specific encryption scheme that turns your password into something that looks like this:
7524248b4d2c9a9eadd3b435c51404eddc5
This is a password Hash. This is what is actually being checked against when you type your password in. It encrypts what you typed and bounces it against what is stored in the Registry and/or SAM File.
You can break this hash password from
SAM File – Holds the user names and password hashes for every account on the local machine, or domain if it is a domain controller.
Location of SAM/Hashes:
You can find what you’re looking for in several locations on a given machine.
It can be found on the hard drive in the folder %systemroot%system32config (i-e C:\windows\system32\config). However this folder is locked to all accounts including Administrator while the machine is running. The only account that can access the SAM file during operation is the “System” account.
The second location of the SAM or corresponding hashes can be found in the registry. It can be found under HKEY_LOCAL_MACHINESAM. This is also locked to all users, including Administrator, while the machine is in use.(GO to Run and Type Regedit and Hit enter, Now scroll to HKEY_LOCAL_MACHINESAM, However you may not access to it.)
So the two (Some other also) locations of the SAMHashes are:
– %systemroot%system32config
– In the registry under HKEY_LOCAL_MACHINESAM
Cracking or Breaking Into Admin Account:
How to get Hashes form SAM file?
Well, Below are the methods to do so:
1) Well, the easiest way to do this is to boot your target machine to an alternate OS like NTFSDOS or Linux and just copy the SAM from the %systemroot%system32config folder.
It’s quick, it’s easy, and it’s effective. You can get a copy of NTFSDOS from Sysinternals (http://www.sysinternals.com) The regular version of NTFSDOS is freeware, which is always nice, but only allows for Read-Only access. This should be fine for what you want to do, however, if you’re the kind of person that just has to have total control and has some money to burn. NTFSDOS Pro, which is also by Sysinternals has read/write access but it’ll cost you $299.
2) You can also get password hashes by using pwdump2 (Google It to get software ~ Search at openwall.com). pwdump uses .DLL injection in order to use the system account to view and get the password hashes stored in the registry. It then obtains the hashes from the registry and stores them in a handy little text file that you can then paste them into a password cracking utility like l0phtcrack or John the ripper (Linux Based works well) also cain and abel can be used.
3) Import Hashes directly from l0phtcrack, and let them open to you by cracking.
Obtained Hashes? Now crack them:
Well, as i have said that these can’t be reversed but somehow automated famous cracking softwares can be used to achieve the target. Yes, it is possible, All we have to do is to have a bit patience. The software will use a lot of strings and will compare these hashes also, Inshort it will decode them.
1) John the Ripper – John the Ripper is to many, the old standby password cracker. It is command line which makes it nice if you’re doing some scripting, and best of all it’s free and in open source. The only real thing that JtR is lacking is the ability to launch Brute Force attacks against your password file. But look at it this way, even though it is only a dictionary cracker, that will probably be all you need. I would say that in my experience I can find about 85-90% of the passwords in a given file by using just a dictionary attack.
2) L0phtCrack – Probably the most wildly popular password cracker out there. L0phtCrack is sold by the folks at @Stake. And with a pricetag of $249 for a single user license it sure seems like every one owns it. This is probably the nicest password cracker you will ever see. With the ability to import hashes directly from the registry pwdump and dictionary, hybrid, and brute-force capabilities. No password should last long. Well, I shouldn’t say “no password”. But almost all will fall to L0phtCrack given enough time.
Making Your Own Password in Windows:
Injecting Password Hashes into the SAM:
Easiest ways to gain Administrator privileges on a machine, is by injecting your own password hashes into the SAM file. In order to do this you will need physical access to the machine and a brain larger than a peanut. Using a utility called “chntpw” by Petter Nordhal-Hagen you can inject whatever password you wish into the SAM file of any NT, 2000, or XP machine thereby giving you total control, just burn the .iso on a disk and use it. I would give a tip like backing up the SAM file first by using an alternate OS. Make a USB disk of linux or Windows Live disk can also work. Go in, inject the password of your choosing. Login using your new password. Do what you need to do. Then restore the original SAM so that no one will know that i was hacked.
You need to have admin access to perform this change from the command line. This is an especially handy trick if you want to change a password on an account but you’ve forgotten the original (going through the Control Panel can require confirmation of the old password).
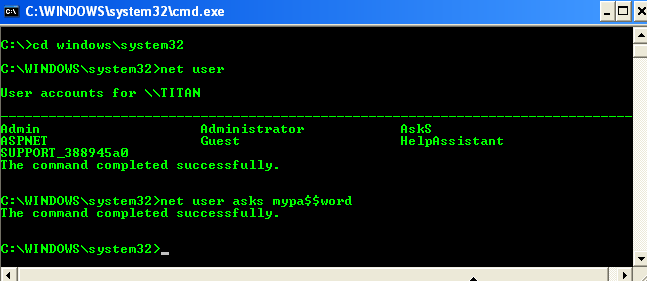
Now we hack Admin Password To verify the user name, by simply typing net user, I get a list of all the user names on that windows machine. Now, go to the command prompt and enter:
cd\
cd windows\system32
net user
If there are people near you and you don’t want them to see the password you type, enter:
net user *
E.g. > net user username *
> Type a password for the user:
> Confirm the password:
Another Easy method, Using ophcrack to Hack into Admin Account:
Ophcrack is a Windows password cracker based on a time-memory trade-off using rainbow tables. This is a new variant of Hellman’s original trade-off, with better performance. It recovers 99.9% of alphanumeric passwords in seconds.
This is a type of offline cracking, Just grab .iso of ophcrack from here. Burn it and enjoy using.
1. Opchrack can crack passwords for Windows 7, Windows Vista, and Windows XP.
2. Ophcrack can recover 99.9% of passwords from Windows XP, usually in a matter of seconds. Any 14-character or smaller password that uses any combination of numbers, small letters, and capital letters should be crackable.
3. Ophcrack can recover 99% of passwords from Windows 7 or Windows Vista. A dictionary attack is used in Windows 7 and Vista.
4. The Ophcrack LiveCD option allows for completely automatic password recovery.
5. LiveCD method requires no installation in Windows, making it a safe alternative to many other password recovery tools.
6. No Windows passwords need to be known to use the Ophcrack LiveCD to crack your Windows passwords.
I think this ophcrack method is far better, Try this one just get a disk and write it, Or else USB disk can also be used.
Some security Tips ~ Making strong passwords:
Now, You might have come to know that how passwords can be cracked, So there are some tips for you.
1) Do not make common passwords like 123456 or the one of your own name.
2) Use @, *, # or other symbols in your passwords to ensure maximum security in this case John the ripper and Ophcrack and also other cracking tools may take long time, it will be frustrating for hacker.
3) Keep changing your password. So, that if long time is taken by one hash to decode, until it decodes you have generated another hash.




